👉Need to reach 100k subscribers : https://youtube.com/@RunssMikaAndroidChannel 👉URGENTLY NEED 1k SUBSCRIBERS : https://youtube.com/@mikachanneloffficial All 3 of my Youtube channels : 👉https://youtube.com/@RunssMikaAndroidChannel 👉https://youtube.com/@mikavosofficial5969 👉https://youtube.com/@mikachanneloffficial WHAT’S NEW UNDERWATER 2024 –… Continue reading
Highlights Battlefield 5 offers an interesting take on World War 2 narratives for fans of the franchise. Multiplayer modes like Firestorm and Grand Operations add tactical depth to… Continue reading
I can feel some kind of sore throat bug coming on. It must be the baleful influence of Creative Assembly’s latest free update for bellowing strategy bonanza… Continue reading
Get one of the hottest fighting game of the year for a historical low price. Nowadays, the latest fighting game installments can cost up to 70€, which is… Continue reading
Apr 25, 2024NewsroomTechnology / Privacy Google has once again pushed its plans to deprecate third-party tracking cookies in its Chrome web browser as it works to address outstanding… Continue reading
💜 No vídeo jogamos o game ROBLOX E COMPRAMOS UMA LAMBORGHINI, MELHOR CARRO DO DUSY TRIP 💜 Olá sejam bem vindo ao canal Só Por causa, com o… Continue reading
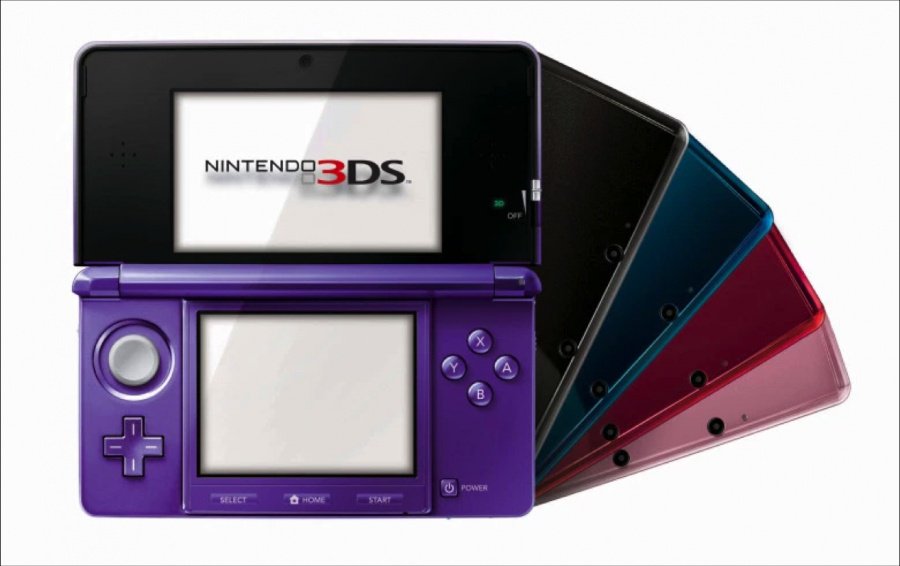
What it most be like to have such a collection like this. The 3DS was one of everyone’s favorite consoles from Nintendo besides the more recent releases of… Continue reading
Collect hundreds of NFL player cards based on real-life counterparts Participate in the draft and find the next big star Play against other enthusiasts from across the globe… Continue reading
Garten Of Banban 7 Officiel français ( fr ) On découvre de nouvelles infos concernant le chapitre 7 de Garten Of Banban ! Si tu veux acheter des… Continue reading
The PlayStation 5 is slowly but surely filling out its library with incredible, story-driven games. These high-budget, visual spectacles are more often than not action games with highly… Continue reading