Cybercriminals are using a network of hired money mules in India using an Android-based application to orchestrate a massive money laundering scheme. The malicious application, called XHelper, is… Continue reading
Category: Hacker news
Mar 04, 2024The Hacker NewsSaaS Security / Vulnerability Assessment A company’s lifecycle stage, size, and state have a significant impact on its security needs, policies, and priorities. This… Continue reading
Mar 04, 2024NewsroomAI Security / Vulnerability As many as 100 malicious artificial intelligence (AI)/machine learning (ML) models have been discovered in the Hugging Face platform. These include instances… Continue reading
U.S. cybersecurity and intelligence agencies have warned of Phobos ransomware attacks targeting government and critical infrastructure entities, outlining the various tactics and techniques the threat actors have adopted… Continue reading
Mar 02, 2024NewsroomSpyware / Privacy A U.S. judge has ordered NSO Group to hand over its source code for Pegasus and other products to Meta as part of… Continue reading
Mar 02, 2024NewsroomCybercrime / Social Engineering The U.S. Department of Justice (DoJ) on Friday unsealed an indictment against an Iranian national for his alleged involvement in a multi-year… Continue reading
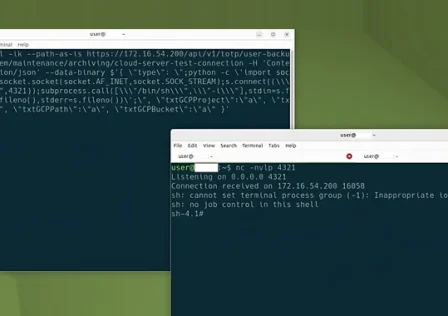
Mar 01, 2024NewsroomLinux / Cyber Threat Cybersecurity researchers have discovered a new Linux variant of a remote access trojan (RAT) called BIFROSE (aka Bifrost) that uses a deceptive… Continue reading
Mar 01, 2024NewsroomPhishing Kit / Cryptocurrency A novel phishing kit has been observed impersonating the login pages of well-known cryptocurrency services as part of an attack cluster designed… Continue reading
More than a decade ago, the concept of the ‘blameless’ postmortem changed how tech companies recognize failures at scale. John Allspaw, who coined the term during his tenure… Continue reading
Mar 01, 2024NewsroomRootkit / Threat Intelligence The Five Eyes (FVEY) intelligence alliance has issued a new cybersecurity advisory warning of cyber threat actors exploiting known security flaws in… Continue reading