The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Friday added four vulnerabilities impacting SimpleHelp, Samsung MagicINFO 9 Server, and D-Link DIR-823X series routers to its Known Exploited… Continue reading
Tag: Adds
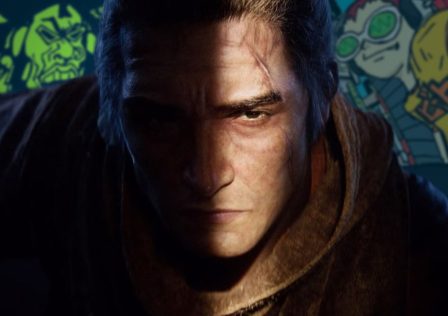
Pearl Abyss continues to impress with the speed of its patches for Crimson Desert. A number of criticisms from the pre-launch period were addressed in the week of… Continue reading
This week, Nvidia’s GeForce Now updates include a round of new games, most of which are new releases, as well as some minor UI tweaks to make the… Continue reading
Raven2 introduces Clash, a 16-guild tournament mode Half Anniversary events include login rewards and missions System updates add Personal Trade and Stella Conversion If I had a penny… Continue reading
The string of significant quality of life improvements for Crimson Desert continues, as the latest update has brought both easy and hard difficulty options, a few new pets… Continue reading
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday added eight new vulnerabilities to its Known Exploited Vulnerabilities (KEV) catalog, including three flaws impacting Cisco Catalyst SD-WAN… Continue reading
There’s something about the forbidden that always tempts us. The knowledge of doing something that’s against the rules, the thrill of potential discovery, and the subsequent fear of… Continue reading
Sekiro and Jet Set Radio are Sekiro Jet Set Radio Mod adds skateboarding and graffiti to FromSoft’s stylish ninja classicmixed in new mod
The Dark Souls trilogy, Elden Ring, and Bloodborne remain the most celebrated and enduring FromSoftware games, yet the far more punishing and agile action of Sekiro shouldn’t be… Continue reading
Image: SEGA Sonic Racing: CrossWorlds has been releasing regular free and paid DLC updates since it launched, and with this in mind, today’s update adds Red from Angry… Continue reading
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday added half a dozen security flaws to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation. The list… Continue reading